 Usually, it’s in the best interests of a botnet operator to let the infection sit on the host machine until finally detected and expunged by the end user. After all, the longer you stay in, the more chance you’ve got of hoovering up useful goodies and infecting other computers.
Usually, it’s in the best interests of a botnet operator to let the infection sit on the host machine until finally detected and expunged by the end user. After all, the longer you stay in, the more chance you’ve got of hoovering up useful goodies and infecting other computers.
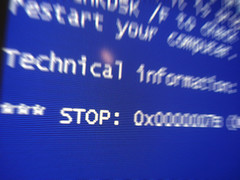
But the worms and trojans that carry the infections often have less subtle capabilities built into them, as was demonstrated last month when the person (or persons) controlling the Zeus botnet used it to completely FuXx0r a hundred thousand windows machines:
Zeus, unlike many other malware programs, managed to make each installation appear different to virus trackers so that it would be more difficult to remove. But Zeus had another interesting feature—one that isn’t terribly uncommon among botnet software, it turns out. A command was built into the software to kos—or “kill operating system”—and it was apparently executed some time last month.
The reason for BSODing 100,000 machines isn’t quite clear, but several security experts have offered up their opinions. S21sec wrote on its blog that those behind Zeus might have wanted more time to exploit the financial data they had harvested by removing the user’s ability to get online and see that money was being transferred.
It may even have been a momentary error, or a flashy cut-and-run. What interests me about this story is that it shows a new potential angle for so-called cyberwarfare – one that could be more easily justified as a politically motivated attack.
Let’s say you could target all the computers belonging to a specific government or corporation; that wouldn’t be too hard to do with a little research into IP numbers and so forth. If you get a good enough infection rate – and knowing how weak most computer security procedures are, even in organisations that should know better, that shouldn’t be too hard a trick either – you could then choose to deep six that organisation’s computer infrastructure at a time of your choosing with the press of a few keys. If your trojan was designed to do nothing else, or its other capabilities were left inactive, that potential could sit unnoticed for some time – until your revolution was ready, perhaps, or your planned day of protest actions, or your stock value raid. To put it in medieval terms, it would be like having a bunch of sleeper-agent sappers spread throughout your enemy’s castle, waiting for the horns of Jericho. [image by Justin Marty]
It’s probably not the sort of thing that an organisation or country with any reasonable military clout would bother deploying, but destructive botnet warfare (as opposed to corrosive attacks, fraud or espionage) will appeal to the geographically-scattered groups who lack the sort of conventional leverage that can be gathered in one place; 100,000 dead PCs won’t bring down a government or kill a company, but it’s going to make a loud and expensive statement for a very small financial outlay.
Botnets still seem predominantly the concern of criminals with a financial motivation, but as the recent Palestinian conflict demonstrated, political factions are waking up to the potentials; when the situationists and anarchists get wind of this stuff, they might start thinking bigger than smashing bank windows or releasing the penguins from your local zoo.